One: carrying the machine into the network into a bane, payment companies and manufacturers are the source!
As we all know, a POS machine that can be used normally by a merchant is generally provided by the bank card acquirer. The acquirer mainly includes: a bank or a third-party payment company. The merchant and the acquirer sign a special merchant agreement, and accept the consumption with the POS machine provided by the merchant. The acquiring business of bank cards. The source of the POS machine of the acquirer is provided by the manufacturer of the POS machine. The safety standard of the manufacturer must generally comply with the UnionPay certification standard before it can be marketed. The manufacturer then develops the terminal according to the recipient's message format, communication method, encryption method, etc. The program is also authorized to install to the pos machine and is ultimately used by merchants.
Since 2012, with the completion of the infrastructure work of the national gold card project, the credit card penetration rate has been rising steadily, the national economic development has accelerated, and the Chinese pos machine market has also developed rapidly. At the same time, the third-party payment company’s acquiring The business is changing with each passing day. In 2014, due to the pre-authorization incident, the mainstream 8 payment companies were stopped from collecting the nationwide, so that a large number of pos machines were shut down and the pos machine manufacturers were slow-moving, while other payment companies seized. Opportunity, agreed with the manufacturer, the payment company began to allow a large number of machines to join the network, regardless of the old machine, or the machine being used, as long as the terminal manufacturer and the payment company platform docked, there are programs available. According to the “Measures for the Management of Outsourcing of Bank Card Receiving Business†promulgated by the central bank, all bank card acquiring institutions should strictly implement the relevant provisions on outsourcing of bank card acquiring business, and must not violate the core business such as customer qualification review, key management, and fund settlement. Outsourcing.
Two: pos machine cutting machine into a trend, in the end who is the victim!
At the beginning, the pos machine master key of the payment company was filled by the manufacturer. Later, some agents sent the key through the data line connection through the mother pos provided by the manufacturer. Nowadays, the manufacturer provides a special filling program. The program can clean the original POS machine program, install the new platform program to facilitate reuse, and finally download the work key online, you can complete the service from one platform to another without changing the POS machine, of course, there are Part of the POS machine is a custom model of the payment company, and its master key is burned into a hardware chip and installed in the POS machine, which is also known as the "underlying key".
As a result, large-scale cutting behavior in the market has become widespread, some because the machine is blocked and can not be used, cut to a new platform, and some because the distribution is too low, and some because the upper level is deducted, and some Purely for vicious competition, specifically to the market to deceive businesses to upgrade lower rates, cut the original machines belonging to other platforms to their own platform for profit, because the manufacturer provides a filling program, which provides convenience for cutting machines, as long as The machine is not a custom model of a third-party payment company, and there is no underlying key to switch platforms.
Up to now, many pos machines without the underlying key have the function of TMS remote update download program. If you want to cut the machine, you don't need to return to the agent or manufacturer. You only need to provide the SN number, and then report it to the manufacturer by secret channel. The manufacturer uses TMS. The remote update download function can clear the original program of pos, update it to the required payment company platform or the program of the Erqing company platform, and complete the cutting machine without knowing it.
What is the difference between such behavior and theft? There are also many uninformed agents who have worked hard for a long time to develop a business volume, but unconsciously their trading volume is getting lower and lower, but they don’t know that there is a black hand behind the scenes! According to the latest news, the three major manufacturers of mobile phone card readers: New World, Ai Chuang, BBpos hand brush, in the market has begun to publicly acquire second-hand hand brush, and claimed to be able to cut the machine remotely, the principle is many Erqing institutions Purchasing a hand brush without the underlying key, of course, there are internal and external collusion, and got some of the underlying keys. According to pos circle estimation, the hand brush cutting machine has been realistic, and the market's festival has been trampled into slag, which can be described as: fire prevention, Anti-theft, anti-cutting machine!
Three: POS machine washing machine decrypted into the industry, cardholder information was recorded!
As a result, market violations have intensified, regulators have been constantly clearing up, and the rise of Erqing institutions. There are quite a few models on the market that pay for the company's platform customization. The models with the underlying key have the need for cutting machines, due to the manufacturer's Terminal sales are gradually being touched by the agent channel and the interests of the company's demand. Many manufacturers have released the underlying secret key, which causes the underlying key of the custom machine to be cracked. It is said that the crack is actually collusion with the manufacturer and the interest replacement is completed. With the scale of cutting machine demand, many folk masters can already complete the hard crack by replacing the chip. It is said that the inorganic is not broken. The original manufacturer propaganda rewards and cracks to prove that the safety of their products is no longer available. Only the folks who are engaged in washing machine decryption There is no advertisement for the machine that he can't break. In the long run, is this the manufacturer's own move to smash his own feet?
In addition, thanks to the help of the manufacturers, as long as there is a program, children above 10 years old who know the computer can complete the operation of washing and cutting machine. Such a large loophole criminal will miss the opportunity, repair pos machine, washing machine Decrypt the trick or buy a second mobile phone and other methods, disassemble the bank card add-on on the motherboard, then find a platform to act as agent, then install the pos machine in the form of free installation of the merchant, or sell the bare metal on the Internet, etc. The bank card information and password information of the cardholder using the POS machine are recorded in real time, and finally the copy card is completed for theft. This kind of crime has been common throughout the country, and it is becoming more and more crazy, and even some companies are indispensable. The employees took the job of taking shortcuts and embarked on the road of crime. Many cardholders and merchants lose a lot of money. Swipe security has become a social issue.
Four: second-hand pos machine trading is hot, making fake and making huge profits!
Many agents, because of the increasingly bad market competition, began to find ways to reduce costs, so the second mobile phone sales of pos machine was born, there is no killing without buying and selling, there is no omnipotent money, there is no source of evil, second-hand pos The machine can be described as extremely low security. There is no underlying key. Any program can be filled freely. Any program can be loaded at will. Even if you want to leave a backdoor program in it, it is not a problem in the hands of the people.
Most small agents are even more indistinguishable from the fact that they have been installed with a side recorder. The consequences of being cheap are harmful to others. Some of the channels that operate bare metal, through the recycling of the second mobile phone of the mainstream bare metal, come back to renovate and deal with it. Buy and sell machines, so you will find that the price of bare metal on the market is so variable, there is no minimum, only lower. In addition, in order to cope with market competition, the payment company sold the agent to the agent at a very low price close to the cost or even lower than the cost. However, after being dismantled by the agent, the new machine was sold to the market at a price lower than the market price. . The chaotic market makes the people of the fish in troubled waters like water. Let countless pos machines without security guarantees fill the whole country, and all of this, everyone has a good heart and a tacit understanding, no one will say.
Five: One machine and more merchants become selling points, and all parties violate vicious competition!
In the case that banks use credit cards more and more rigorously, for those who have a rigid demand for credit card as a low-interest financing channel, the card has become a professional paid service business, multi-industry and multi-frequency consumption is An important criterion for maintaining credit card credit, but a credit card cannot be repeatedly consumed by the same POS machine and the same merchant, so as to prevent the card issuer from thinking that there is a suspected credit card and a credit limit.
However, multiple pos machines mean higher costs. In order to meet this demand, one machine and multiple merchants and one machine and multiple programs have emerged. The pos terminal usually has one terminal only when it meets the UnionPay certification standard. SN number, a SN number is bound to a merchant to meet the requirements of risk management and data confidentiality. However, there are terminal manufacturers such as Shida's WP70, which is equipped with 10 virtual SN numbers, as well as other brands such as Xinguodu, Xinnuo, Huazhirong, New World, etc. The pos terminal can generate SN number software and is sold and marketed. Spread through.
Everyone knows that because the payment company's platform allows the machine to be connected to the network, as long as the agent reports the SN number to its system, and then the merchant's order, the pos terminal installs the program of its platform, and finally binds the merchant number and terminal number. Normal use, at the same time, some payment companies allow one card to be dismissed, or an illegal person to disembark, or deliberately relax the audit of the authenticity of the business, allowing the agent to submit the data of the PS application, allowing one to apply multiple false merchants It uses a number of MCC codes from different industries to complete the so-called multi-operator, allowing users to change the use of different merchants to achieve the purpose of raising cards. This is the so-called multi-operator.
Of course, under the current strict supervision, each of them has begun to put an end to the behavior of one machine and many merchants. However, there is always a modern X-control company that claims to be a state-owned enterprise. It publicly supports one machine and multiple merchants and becomes its selling point. There are also other Second-rate payment companies in order to semi-publicly support multi-merchant merchants, this is no longer pointed out here. Such as the implementation of the company's 10 SN number as a product selling point, can be confirmed to be illegal, for some brand terminal SN number free to produce and buy, at least prove that there are technical loopholes or the existence of internal personnel are driven by interests Collusion with outsiders, these acts are a serious disruptive market order, depending on the security of malicious activities.
The multi-program is simpler, and the POS terminal can be regarded as a smart terminal. It can install multiple authorized programs, just like many APP applications in mobile phones. On most payment platforms, one person is not allowed to apply for multiple applications. In the case of merchant rates, in the hands of agents with multiple payment platform programs, install the programs of multiple platforms into one pos terminal without the underlying key, and then pay multiple to the same person. The platform applies for different merchants. When you use the program, you can implement one machine and multiple programs, one machine, 10 merchants, or even 100 merchants!
This can meet the needs of the family of card-raising, and can sell at a high price to earn profits. According to the rules of UnionPay, one machine and one yard, and the common sense in the industry, the basic risk control requirement for the merchants of the private settlement is that it is normal for a private settlement account to apply for a merchant number with a business license, and a private settlement. Accounts can have multiple business licenses. Multiple merchant numbers are obviously fake merchants. One machine can have 100 merchants. This wonderful phenomenon comes from the related one-off agency’s one-eyed one-sided side-bounce behavior, regardless of the behavior. It is a multi-merchant of traditional pos, or a multi-rate of hand-brushing is a very obvious violation!
Many violations, many violations, facing the gray phenomenon of the entire industry chain, facing the country's close to a million pos machines without security, many second clear machines that use plaintext to transmit data information, and many other technical details I will not elaborate here one by one. I have time to write another article to tell you how to leave the back door in the pos machine without the underlying key, cough, don't be joke! Probably the principle:
KEK:
Purpose of the KEK key: KEK is actually a key used to encrypt and decrypt the master key. The master key that is imported is the ciphertext encrypted by KEK, and the vendor decrypts the master key ciphertext by using kek in the SDK.
KEK encrypts the master key with the 3DES algorithm
KEK, master key, work key
The general practice is that the acquiring platform provides the master key ciphertext and KEK to the manufacturer, and the terminal is factory-fired; when the merchant binds the terminal, the working key is downloaded. So the key mechanism should be planned, look at this KEK and the master key, is it the factory machine will burn. Generally, most APKs provide this master key file to the manufacturer, and a SN number corresponds to a master key. (The second-hand terminal's underlying key is cracked, and one machine and multiple merchants are not.)
Master key: used to decrypt the work key ciphertext obtained by sign-in.
Work Key: Includes PinKey (for password encryption) and MacKey (for message encryption)
Check in: get pinkey, mackey, batch number
Signing out: First batch settlement, then sign back, otherwise the batch number will not be updated.
Batch settlement: send the local pos terminal transaction flow to the server, if it passes the verification, you can sign the refund, otherwise you need to send the transaction details on the batch.
Batch delivery: batch settlement verification failed, send local transaction details to the server for comparison.
Password encryption principle: use the terminal master key to decrypt the pinKey obtained by signing in, obtain the plain key of the pinKey password, and then participate in the PIN block encryption with the password plaintext.
Calculating MAC messages is also the same
PIN: Personal Identification Number, which is the password.
PAN: Personal primary account
The PIN BLOCK format is equal to the PIN bitwise XOR PAN:
18-digit bank card password encryption example
For example: The plain text PIN is: 123456,
Assumption: PAN 3456 78 on the magnetic card
Intercepted PAN
The PAN used for PIN encryption is: 0x00 0x00 0x67 0x89 0x01 0x23 0x45 0x67
PIN BLOCK is: 0x06 0x12 0x34 0x56 0xFF 0xFF 0xFF 0xFF
XOR: 0x00 0x00 0x67 0x89 0x01 0x23 0x45 0x67
The result is: 0x06 0x12 0x53 0xDF 0xFE 0xDC 0xBA 0x98
16-bit bank card number password encryption example
Assumption: PAN 3456 on the magnetic card
Intercepted PAN
The primary account used for PIN encryption is: 0x00 0x00 0x45 0x67 0x89 0x01 0x23 0x45
PIN BLOCK is: 0x06 0x12 0x34 0x56 0xFF 0xFF 0xFF 0xFF
XOR: 0x00 0x00 0x45 0x67 0x89 0x01 0x23 0x45
The result is: 0x06 0x12 0x71 0x31 0x76 0xFE 0xDC 0xBA
There are a few more points to note:
1: Most of the current flow cards circulating on the market are not standardized for pos machines. There are too many communication flow cards. Should a specific pos card be specified? Where is the POS machine report where it is, can not be transferred to use, its communication card should be local, not the national, this is the laissez-faire of the acquirer, management dereliction of duty!
2: It is illegal to decrypt the washing machine of POS machine. The manufacturer has the responsibility and right to sue for infringement of intellectual property rights and harm to safety!
3: Many models of pos machine manufacturers do not have the function of tampering machine or fail to meet the standard. This is illegal. According to the standard of UnionPay safety certification, this cannot be passed, but the reality is how to remove it, the manufacturer should Take responsibility!
4: Some of the regulatory agencies have been seriously derelict, the old models have been cleaned up slowly, the technical standards of the new models are backward, the market supervision is ignored, the uncertified pos terminals are everywhere, the certified production environment is seriously mixed, and there are major defects in the safety of laissez-faire. The second mobile phone is rampant in the market, and the supervision is seriously inaction. I want to report Xi Da.
The purpose of this article is to reflect the problem to the society. As an important part of the entire bank card acquiring industry chain, the pos terminal manufacturers, as the arms dealers of the market war, who will supervise them? Pos Xiaobian has knocked down so many words, and then knocked a few more words:
Some pos machine manufacturers, what are you doing?
Hardware supervision units, what are you doing?
What are you doing for the illegal payment companies?
The small preparation of this industry white paper can be said to offend most of the practitioners, but we have witnessed history, history needs to be recorded, and vicious commercial competition will bring devastating blow to the market, leaving only It is a scar, the industry needs healthy development, competition needs to be dominant, cardholders are innocent, merchants are innocent, entrepreneurial investors are innocent, false is false, money is money, shame is not shame, Even if the dark clouds cover the sky, and when the weather is sunny, it will be blue! And we are ready to be enemies with the world, waiting for the weather!
Choicy is professional esthetics equipment manufacturer, producing dr pen microneedling reviews,dr pen ultima m5,best Microneedling Pen for home use,best professional microneedling pen 2020,dermapen roller,dermapen 4 for sale,microneedling pen before and after, derma pen needle, dermapen needle cartridge, microneedling 12 pin, dr pen a6 cartridges. To view the full range of laser machines that we have available, you are welcome to contact us to have a video online meeting to see the machines up close and personal. Also, please send your requirements with a detailed list including the style/item and quantity you require. We will then send our best prices to you. Manufacturers Machine Operation training is included with all machines and no previous experience is required.
Application area
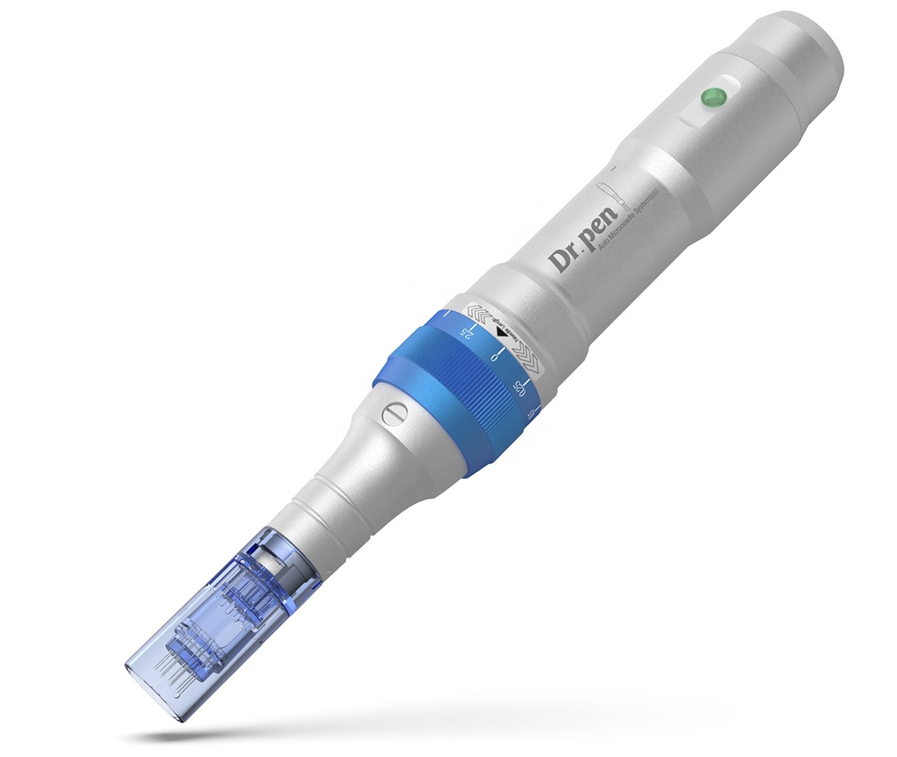
Dr. Pen A6
Derma Pen Needle,Dermapen Needle Cartridge,Microneedling 12 Pin,Dr Pen A6 Cartridges
Choicy , https://www.choicygroup.com